Let's Encrypt's ROOT Certificate expired!

And it happened, yesterday (30th September, 2021), the root certificate that LE was using expired. How should I deal with this?. Well, it depends. If your OS is recent probably you just need to update the package where the ca-certificates are, but total different story if your OS is as old as WW1.
In my case I've a Debian7 using and comsuming some LE certs in both ways so I woke up this morning with the smell of alert in the atmosphere. After reading some literature here and there and talked about it with some mates, decided to manually update the certificate. I was forced to proceed in that way because the package updates for deb7 are totally out of date (or even closed I'd say).
We can see the error here:
$ openssl s_client -host oscarmlage.com -port 443 -showcerts CONNECTED(00000003) depth=2 C = US, O = Internet Security Research Group, CN = ISRG Root X1 verify error:num=20:unable to get local issuer certificate verify return:0
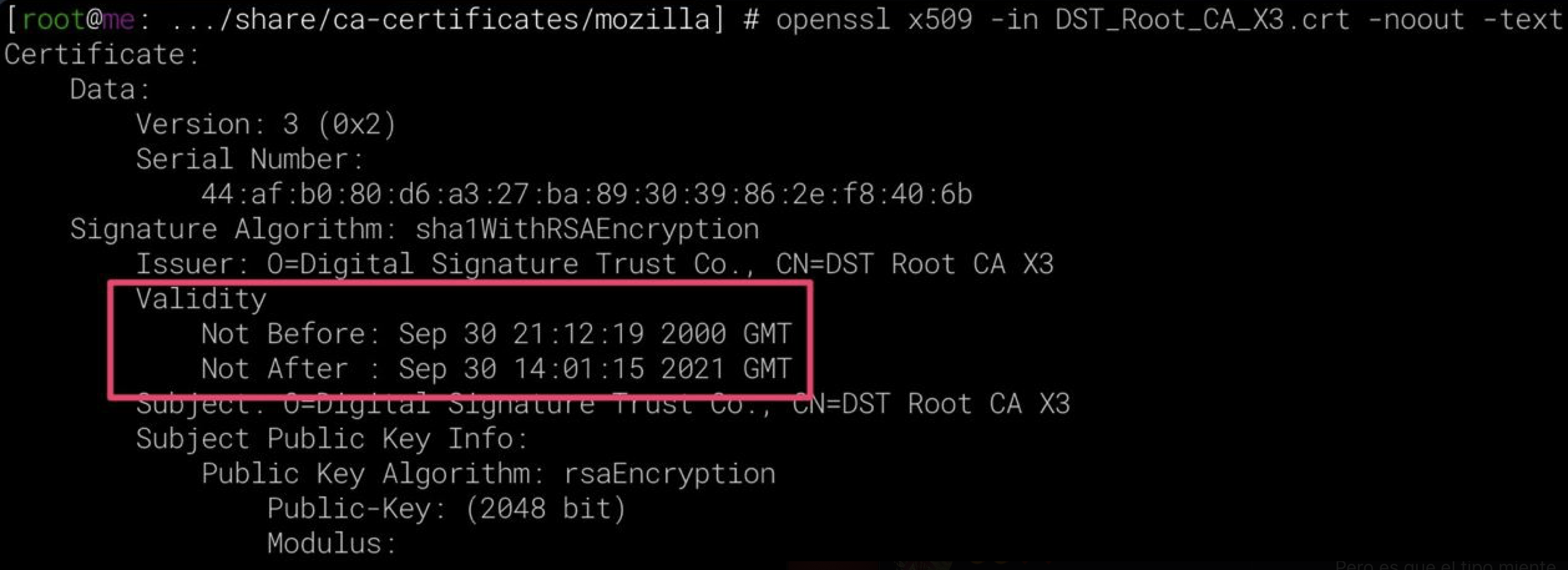
So, first step is to allocate the file where the LE cert is: DST_Root_CA_X3.crt, placed in /usr/share/ca-certificates/mozilla/. Once we found it we can ensure that dates are the root of the issue, we're looking for this one (openssl x509 -in DST_Root_CA_X3.crt -noout -text):
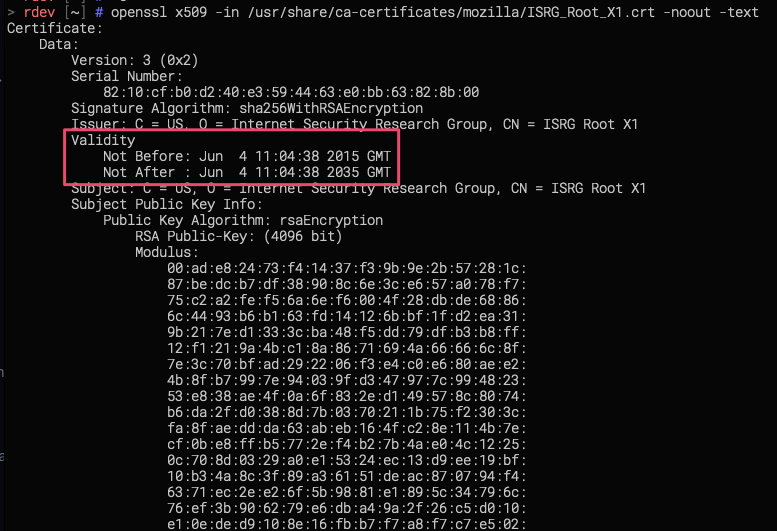
Ok, we're on the way, next step is to find out where is the equivalent cert in some other more recent Debian (maybe a VM can help here), we're looking for ISRG_Root_X1.crt in /usr/share/ca-certificates/mozilla/, we can ensure it's the one we're looking for here (openssl x509 -in ISRG_Root_X1.crt -noout -text):
Take a look to the X509v3 Subject Key Identifier, in both cases (DST_Root_CA_X3.crt and ISRG_Root_X1.crt) it should have the same key:
C4:A7:B1:A4:[...]:60:85:89:10
Now that we already have them handy, we need to copy the good one, remove the older other in the affected machine and refresh the certificates:
$ scp user@newerhost:/usr/share/ca-certificates/mozilla/ISRG_Root_X1.crt /usr/share/ca-certificates/mozilla/ $ mv /usr/share/ca-certificates/mozilla/DST_Root_CA_X3.crt /tmp/
$ echo "/usr/share/ca-certificates/mozilla/ISRG_Root_X1.crt" >> /etc/ca-certificates.conf $ vim /etc/ca-certificates.conf # remove the /usr/share/ca-certificates/mozilla/DST_Root_CA_X3.crt line $ update-ca-certificates --fresh Clearing symlinks in /etc/ssl/certs...done. Updating certificates in /etc/ssl/certs... 171 added, 0 removed; done. Running hooks in /etc/ca-certificates/update.d....done.
And we can test if it works now:
$ openssl s_client -host oscarmlage.com -port 443 -showcerts CONNECTED(00000003) depth=2 C = US, O = Internet Security Research Group, CN = ISRG Root X1 verify return:1 depth=1 C = US, O = Let's Encrypt, CN = R3 verify return:1 depth=0 CN = oscarmlage.com verify return:1
Of course, best approach in this kind of stuff is proceed with the proper update, upgrade, etc... but not always is doable/possible - there are many reasons I won't mention now -. So I hope this post helps if you're in a situation where the updates are not the solution.
Note, the certs itselves (the old and the new one) can be found here:
Cheers!